Important facts about NIS 2
- What is NIS 2?
- NIS 2 is an EU directive that significantly tightens cyber security and resilience for critical and important facilities.
- When does NIS 2 apply?
- NIS 2 has been in force throughout the EU since 16.01.2023. The transposition deadline for member states ended on 17.10.2024. In Germany, the transposition law has been in force since 06.12.2025.
- Who is affected by NIS 2?
- This affects organizations in critical sectors (e.g. energy, transport, health, water) and other important areas such as IT services, postal services and parts of manufacturing.
- What are the most important obligations?
- Higher security measures and a reporting process in stages are required: 24h early reporting, 72h follow-up reporting, 1 month final report.
- What is the threat of violations and what is the goal?
- There is a threat of high fines (up to €10 million or 2% of global turnover) and more responsibility at management level. The aim is more resilience, better supply chain security and EU-wide comparable standards.
Abstract
NIS-2 is the most important EU regulation on cyber security. It obliges "essential" and "important" institutions to manage cyber risks in a structured manner, implement appropriate protective measures and report serious incidents within clear deadlines, with a particular focus on the supply chain. In Germany, the implementation has been in force since December 6, 2025. Registration and reporting are carried out via the BSI portal, which was activated at the beginning of 2026. Whether a company is affected depends primarily on the sector, size and special cases: In addition to classic KRITIS areas, IT service providers, parts of industry, logistics-related sectors and certain platform models can also fall under this. Requirements are also often passed on to service providers and suppliers via contracts. In terms of content, it is not just about "more IT security", but about a functioning overall package of prevention, detection, response and recovery, including measurable effectiveness and clear rules for critical providers. Anyone who submits reports too late, is unable to provide evidence or does not have the supply chain under control quickly exposes themselves to an increased risk of audits and fines.
Current updates on implementation in Germany
In Germany, the NIS 2 Implementation Act has been in force since 06.12.2025. Previously, Germany, like several other EU states, had not fully notified the implementation deadline on time, which is why the EU Commission launched infringement proceedings.
What is the NIS-2 Directive?
Definition of the NIS-2 Directive
The NIS 2 Directive(Directive (EU) 2022/2555) is the central EU regulation on cybersecurity. It obliges certain companies ("essential" and "important" entities) to systematically manage cyber risks and report serious security incidents in accordance with fixed requirements.
A key point is supply chain security: NIS-2 explicitly includes direct suppliers and service providers, such as cloud and SaaS providers, IT providers, managed service providers and software suppliers. This makes supplier management a compliance obligation.
As NIS-2 is a directive, it must be transposed into national law by each EU member state. Therefore, details differ in practice depending on the country, for example in terms of responsibilities, processes and portals.
Background and origin
NIS-2 is the further development of the 2016 NIS Directive and was necessary because cyberattacks have become more professional and no longer only affect traditional critical infrastructure. Digital dependencies, such as cloud services, remote maintenance, IT service providers and software supply chains, are particularly important today. The NIS 2 Implementation Act expands the circle of affected companies and makes supply chain risks a mandatory topic.
Timing:
- End of 2022: NIS-2 is adopted and published in the EU Official Journal.
- 17.10.2024: Transposition deadline for the Member States.
- Nov 2024 / 07.05.2025: EU Commission launches infringement proceedings (letter of formal notice, later reasoned opinion, also against Germany).
- 05./06.12.2025 (DE): Publication and entry into force of the German transposition law.
- 06.01.2026 (DE): Activation of the BSI portal for NIS-2 registration.
In parallel to national implementation, the EU ensures that important basic digital services, such as the cloud, data centers, IT service providers and internet services, operate according to similar minimum rules in all EU countries.
This is particularly clear when it comes to supply chain security: companies should actively keep an eye on their most important IT service providers. This includes a list of central providers, clear security requirements, appropriate contractual rules, regular verification and fixed processes for quickly closing security gaps.
Implementation in Germany
Germany has implemented NIS-2 nationally: The implementation law has been in force since 06.12.2025 (promulgated on 05.12.2025). For affected companies, this involves specific obligations such as risk management, documentation, registration and incident reporting.
The BSI portal, which was activated at the beginning of 2026 and is used for registration and reporting, is practical for companies.
Main objectives of the NIS 2 Implementation Act
Anchoring cyber security as a management and governance issue
NIS-2 makes it clear that cyber risks are not just an IT issue, but are the responsibility of management. The EU Commission expressly emphasizes the accountability of top management.
Increase resilience: not only prevent, but also persevere and get back on track
The aim is for companies to remain capable of acting throughout the entire course of a security incident, from risk analysis and prevention, through detection and response, to restart and crisis management. This is particularly crucial in supply chains: if a service provider fails, the most important processes should not automatically fail because contingency plans and recovery routes are defined in advance.
Securing supply chains: Third parties as a mandatory part of risk management
NIS-2 is intended to make attacks via the supply chain more difficult. To achieve this, it is not enough to just protect your own IT. Central service providers and suppliers must also be actively managed, with clear security requirements, appropriate contractual rules, evidence and regular checks. Supply chain security is therefore not just an IT task, but also affects purchasing, legal and supplier management.
Faster, more standardized response to incidents - also across borders
A key objective is to ensure that relevant incidents are dealt with more quickly where coordination is possible and that major incidents can be handled in a coordinated manner across the EU. The CSIRTs network andEU crisis coordination via EU-CyCLONe exist for this purpose.
More harmonization in the internal market (less patchwork)
Companies operate across borders, especially their service providers. NIS-2 aims to make minimum requirements, supervision and cooperation more consistent across the EU. The fact that implementation was nevertheless delayed in many countries and the Commission had to follow up formally shows how important this harmonization issue is.
What is new compared to NIS 1?
Goal & basic principle
NIS 1 (2016) was the first EU framework for cybersecurity. It mainly affected operators of essential services and some digital providers, with mandatory security measures and reporting of serious incidents.
NIS 2 builds on this, but goes much further: it places greater emphasis on risk-based management and resilience (prevent, detect, respond, recover) and explicitly includes the supply chain.
The most important innovations
NIS 1 focused primarily on traditional critical services and a few digital providers. The NIS 2 Implementation Act goes much further, as it now covers 18 sectors. This is intended to reduce gray areas, better align the rules in the member states and, above all, map today's digital dependencies more realistically.
The NIS 2 Directive is much more specific than NIS 1. It states more clearly what a company must do as a minimum to have cyber risks under control, for example: handle security incidents in a structured manner, have emergency plans, close security gaps regularly, train employees, encrypt data, control access properly and secure important accounts with multi-factor login. This is helpful because auditors have less room for interpretation later on and it is clearer what is being measured.
NIS 2 explicitly makes supply chain security mandatory. This refers not only to the company's own IT, but also to cooperation with direct suppliers and service providers, such as cloud providers, IT service providers or software partners. In practice, this means that security requirements must be clearly defined and contractually regulated, suitable evidence should be available, information must flow quickly in the event of incidents and clear rules are needed on how to deal with security gaps at the service provider.
NIS 2 anchors governance much more firmly: management bodies must approve and monitor measures. There is also a training requirement for members of management bodies so that they can assess risks and manage decisions in a comprehensible manner. This is a clear step away from "IT will do it" and has a direct impact on the supply chain, as budgets, contracts, provider strategies and priorities are management decisions.
The NIS 2 Implementation Act introduces a tiered reporting procedure and strengthens enforcement: supervision is more proactive for significant institutions and more ad hoc for important institutions. In addition, there are harmonized EU-wide fine limits: up to €10 million or 2% of global turnover (depending on the category) or up to €7 million or 1.4%.
Which companies are affected?
Categories & logic: sector, size, special cases
The basic logic of NIS-2 can be broken down into three test steps, even if the details may vary depending on the member state in the national implementation:
→ Sector: Are you active in one of the sectors covered by NIS-2 (e.g. energy, health, digital infrastructure, manufacturing, etc.)
→ Size: Do you typically reach the thresholds above which NIS-2 often applies (in practice often "medium-sized and large companies", e.g. from approx. 50 employees or > €10 million turnover, depending on the national structure and classification)?
→ Special cases: Some companies fall under NIS 2 even if they are small, especially for certain basic digital services. In addition, Member States may include other companies in individual cases if they are particularly important for supply or security or if many others are dependent on them.
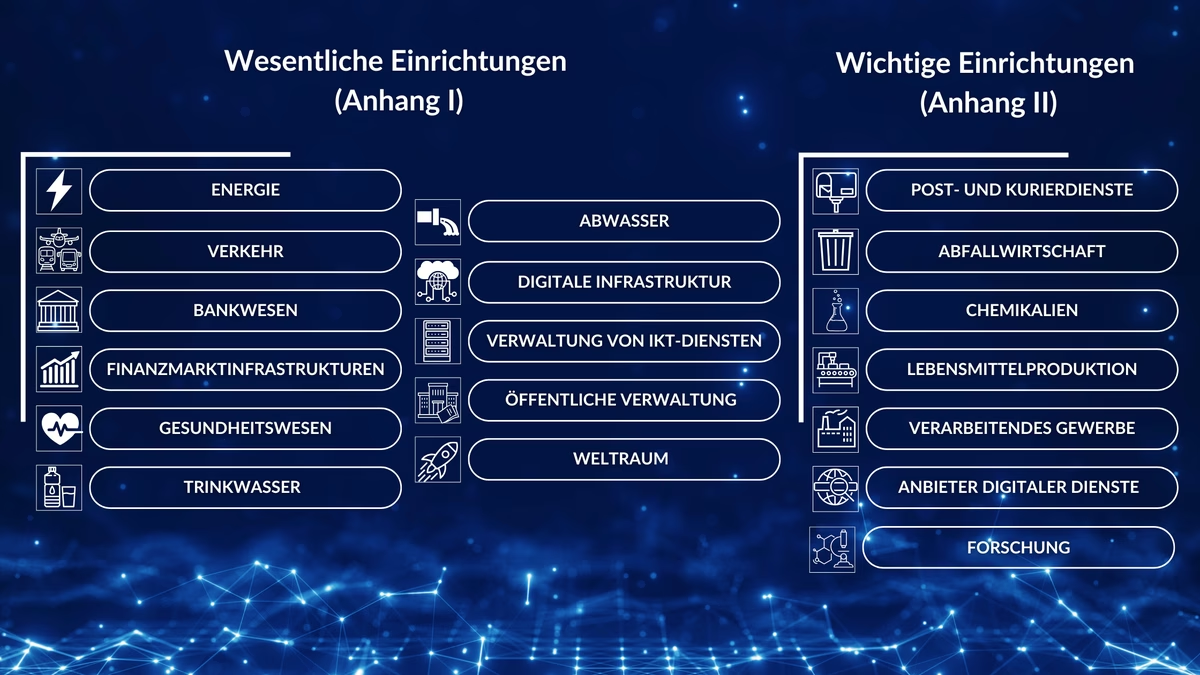
EU system: At EU level, NIS 2 distinguishes between "essential" and "important" facilities. In principle, similar obligations apply to both: Cyber risks must be managed and serious incidents must be reported. The difference is particularly evident in practice: essential entities are usually subject to stricter, sometimes preventive, supervision and the scope of sanctions is generally higher.
NIS 2 implementation in Germany: In Germany, the national implementation has been in force since 06.12.2025. As at EU level, classification is based on sector, company key figures and special cases. The German system uses categories such as "important" and "particularly important" facilities.
Supplier focus: Even if companies themselves are not directly affected by NIS-2, they can still be affected, for example indirectly via customers. For example, if a company is an IT service provider, cloud or hosting provider, managed service provider, software supplier, maintenance or remote access service provider or a critical logistics or platform partner, NIS-2 obligations are often passed through: via contracts, tenders, security questionnaires, verification requirements and incident reporting requirements.
Who is affected? Sectors briefly explained
NIS-2 makes a rough distinction between particularly critical areas and other critical areas.
Typically high criticality (often "substantial"):
- Energy
- Traffic, transportation
- Banks & financial market infrastructures
- Health
- Drinking water & waste water
- Digital infrastructure (e.g. cloud, data centers, DNS/TLD, CDNs, trust services)
- ICT service management (e.g. managed services, managed security services)
- Public administration
- Space
Other critical sectors (often "important"):
- Postal and courier services
- Waste management
- Chemistry
- Food
- Manufacturing industry (e.g. mechanical engineering, electronics, vehicle construction)
- Digital providers (e.g. online marketplaces, search engines, social networks)
- Research
Why this is crucial for supply chains
Many companies underestimate their impact because they do not see themselves as "classic CRITIS". However, it is often in production, logistics, platform operations or IT services that the greatest digital dependencies and therefore obligations (direct) or requirements from customer relationships (indirect) arise.
Practice check: typical examples
IT service provider & provider
Many companies underestimate the fact that even those who are not "KRITIS" can fall under NIS-2 as digital service providers, such as cloud providers or data centers. These providers are often critical for many customers at the same time and are therefore a particular focus of attention. In this role, contractual obligations are often expected, e.g. 24/7 contact, rapid incident information, regulated patch and vulnerability management, evidence and clear rules for subcontractors.
Manufacturing companies
NIS 2 also covers parts of the manufacturing industry. This can also affect medium-sized industrial companies, especially if they play a key role in supply chains or operate highly digitalized or automated production. Frequent risks arise via ERP/EDI interfaces, logistics IT, remote maintenance, production control updates and external service partners. It is precisely such dependencies that should be actively managed under NIS 2.
Chemicals, food, waste management, post, courier
These sectors are often underestimated, but are named as critical sectors in NIS-2. The decisive factors here are less high-tech issues than the consequences of an outage for supply and operations. A strong dependence on a few service providers is also typical. If a key partner fails, this can quickly affect operations and trigger a reporting obligation.
Digital business models
NIS 2 also explicitly mentions certain online platforms. This does not refer to every online store, but primarily to platform models such as marketplaces with third-party providers. Such platforms are usually heavily dependent on external services, for example cloud infrastructure, payment service providers, identity and login services or external DevOps and security services. This is precisely why the management of service providers and suppliers plays a particularly important role for them.
Obligations: What does NIS-2 specifically require?
Risk management & security measures
NIS 2 requires affected institutions to secure their IT in such a way that central systems run stably and incidents cause as little damage as possible. In Germany, this is set out in Section 30 BSIG, including a minimum catalog of ten risk management measures.
In practical terms, the obligations can be divided into four areas: Prevention, detection, response and recovery.
1) Prevention
By prevention, NIS 2 means above all: recognizing risks early, keeping attack surfaces small and securing particularly important access points well. This includes a solid risk analysis and an IT security concept, secure rules for purchasing, developing and operating systems as well as topics such as encryption, personnel security, clear access rights and an overview of all important IT devices and applications. Multi-factor authentication is also explicitly mentioned, especially for critical accounts and access points.
- IAM (Identity & Access Management): describes rules and systems that control who can access which IT resources (incl. roles, authorizations, recertification).
- MFA (multi-factor authentication): additional security when logging in, particularly relevant for admin accounts and remote access.
- Secure development or secure procurement: Security is "built in" during purchasing and development (e.g. secure configurations, update capability, supplier specifications, acceptance checks).
2) Recognize
NIS 2 expects that security incidents do not simply "slip through". In practice, this means that clean logging, continuous monitoring and reliable vulnerability management are required to ensure that security gaps are quickly identified and rectified. Furthermore, it is not enough to have these measures on paper; they must work in practice and be checked regularly.
- Logging or monitoring: logs of security-relevant activities (e.g. admin actions, login attempts, changes to critical systems) plus evaluation and alerting.
- Vulnerability management: Process for identifying, evaluating, prioritizing and resolving vulnerabilities in a timely manner (patching or mitigation). The BSI emphasizes vulnerability management as a central component of the NIS-2 security measures.
3) React
NIS 2 requires that companies not only detect security incidents, but also handle them properly: recognize, contain, check causes, secure traces, control communication and implement concrete countermeasures. In the German § 30 BSIG, this management of security incidents is therefore explicitly mentioned as an obligation.
This is directly related to the reporting obligations (24 hours / 72 hours / 1 month). Without clear processes, i.e. fixed roles, escalation channels, 24/7 availability and defined decision criteria, these deadlines can hardly be reliably adhered to in practice.
4) Resilience
A key aspect of NIS 2 is resilience: a security incident should not automatically lead to a long standstill. This is why § 30 BSIG specifies the maintenance of operations as a minimum requirement, for example through backups, recovery plans and crisis management. BCM (Business Continuity Management) refers to precisely this ability to continue critical processes despite disruptions or to restore them quickly.
Cross-section: effectiveness monitoring and continuous improvement
NIS-2 is not a "project with an end date". The minimum catalog explicitly contains procedures for evaluating the effectiveness of risk management measures. This means that measures must not only exist, but also function in a comprehensible manner (e.g. via tests, exercises, key figures, audit results).
NIS 2 makes supply chain security an integral part of cyber risk management, and in Germany this applies to all
Supply chain & service providers
The starting point is typically a supplier and service provider directory that not only shows "who supplies what", but above all the cyber relevance:
- Does the provider have access to internal systems or admin accounts?
- Does it operate business-critical platforms (e.g. cloud workloads, email, ERP, identity)?
- Can a failure of the service provider significantly disrupt the provision of services?
- Is it a "single point of failure" or are there alternatives?
The BSI takes up this logic in its NIS 2 support documents on the supply chain and emphasizes the need for a structured approach.
For critical IT service providers, a kind of "baseline" is often expected in practice, i.e. a minimum set of security requirements that must apply regardless of the individual case. This typically includes
- Access protection: MFA for remote access and privileged accounts; clear role and rights concepts (least privilege).
- Vulnerability & patch management: defined processes, prioritization of critical gaps, deadlines, SLAs and transparency about how security gaps are handled.
- Incident cooperation: contractually regulated information obligations and defined contact channels (incl. 24/7 availability) so that reporting deadlines can be met.
- Business continuity: Proof of backup, recovery, restart targets and regular tests (BCM reference).
- Proof and transparency: suitable evidence (e.g. test reports, certifications, security reports) that make the security level comprehensible.
Supply chain risks arise particularly often where third parties have privileged access or subcontractors are used in the background.
- PAM (Privileged Access Management): Process for securely controlling admin access, e.g. time-limited rights, approvals and logging. The aim is to make privileged (including external) access controllable.
- Subcontractors: If service providers use other providers, transparency and rules are needed to ensure that risks are not passed on unnoticed.
- Proof of security: Verifiable evidence is often required, such as certificates, reports, pen test summaries or security KPIs.
NIS-2 also explicitly requires procedures for assessing effectiveness. This applies to supply chains as well as internal measures. This makes supplier security a continuous process. In practice, regular reassessments and comprehensible key figures are typical, for example:
- Patch SLA compliance / time to fix critical vulnerabilities
- Incident response times / speed of information to customers
- Results of restore tests / BCM exercises
- Number and severity of open findings from audits or security reviews
Notifications and registration
Reporting obligations - who does what and when?
NIS-2 relies on a three-stage reporting system for incidents. The time at which knowledge is obtained is decisive: The deadlines run from the moment a facility learns of a significant security incident and not only when all the details have been clarified. Reports are sent to a joint reporting office set up by the BSI together with the BBK.
What is considered a "significant security incident"?
An incident is considered significant if it noticeably disrupts operations or causes or could cause major financial damage. This also applies if it could cause considerable material or immaterial damage to others, i.e. customers, partners or third parties.
The three stages at a glance (BSIG § 32):
Early initial notification (24 hours at the latest)
An initial report must be issued after 24 hours at the latest. This is primarily about a quick assessment: is there anything to suggest that the incident was caused deliberately and could it have an impact beyond Germany?
Follow-up report / notification (no later than 72 hours)
The next report follows within 72 hours. This supplements or corrects the first report and provides an initial assessment of how serious the incident is and what impact it will have. If available, indicators of compromise ("IoCs") can also be sent, i.e. technical indications that point to an attack, such as conspicuous IP addresses or domains, malware hash values or suspicious log entries.
Final notification (no later than 1 month after the 72h notification)
A final report is due no later than one month after the 72-hour report: detailed description, cause, type of threat, remedial measures and any cross-border effects. If the incident is still ongoing at this point, a progress report must be submitted first. The final report follows after processing has been completed.
Interim messages: In addition, the BSI can request interim reports on status updates during an ongoing incident.
Special case KRITIS operators: Operators of critical systems must also specify in their notification which system or critical service is affected and how the incident affects this service.
Why this is organizationally different internally than many previous incident processes: The stage model requires a reliable initial assessment to be available at a very early stage (What is affected? How bad? Which services? Which indicators?). In practice, this usually means Incident response (technology), management situation picture, communication, PR, legal, compliance and, depending on the data reference, data protection must be interlinked in such a way that information that can be used for decision-making and reporting can be brought together within 24/72 hours.
Registration & internal contact point
Registration is primarily about clear master data and reliable contact information: Name and legal form, address, e-mail and telephone number, as well as the public IP address ranges. In addition, there is information on the classification, i.e. sector or industry and the EU countries in which the respective services are offered.
Operators of critical systems must also provide more details, for example which critical service is affected, which critical components are used, the system category, relevant supply figures and the location. In addition, a contact point is required that can be reached at any time in the event of an emergency.
NIS 2 is designed to ensure that authorities can reach someone quickly in the event of an incident. The contact details from the registration are crucial for this. For KRITIS, a contact point that can be reached around the clock is also required.
In practice, this usually means that a clearly designated point of contact is needed within the company to mediate between incident response, management and communication. This is particularly important if the incident involves a service provider or provider because the initial information often originates there and needs to be quickly collated internally.
The BSI activated the next step towards NIS 2 registration via the BSI portal at the beginning of 2026, with reference to around 29,500 affected companies.
If something changes after registration, the information must be updated, in many cases immediately, but at the latest within two weeks of the change becoming known. For KRITIS, regular reports are also required depending on the key figures or components used.
Interaction with other obligations
1) GDPR: Cyber incident ≠ automatic data protection incident
An NIS 2 incident can also be a GDPR data breach if personal data is affected. In this case, the data protection authority must usually also be notified within 72 hours. The BSI points out that NIS 2 notifications must therefore often be coordinated with other obligations, such as the GDPR.
2) Information from customers or recipients
In addition to reporting to the authority, the BSI may require that customers or users are informed quickly if an incident could affect performance, including via a notice on the website. This is particularly important if the trigger lies in the supply chain, for example with a service provider.
3) Sector-specific regimes and contractual chains
Depending on the industry, additional reporting obligations may apply. Irrespective of this, NIS 2 requirements are often passed on contractually in the supply chain: Service providers must provide information quickly so that their own 24h/72h deadlines can be met at all.
Supervision & Sanctions
Who monitors?
In Germany, the BSI is primarily responsible when it comes to the supervision of NIS 2 obligations, i.e. for important and particularly important institutions, KRITIS operators and also for the federal administration. For some digital services that are often used across borders, such as DNS, TLD or certain cloud and platform services, the authority with lead responsibility in the EU also plays a role.
As a distinction is made between essential and important facilities, there are also different types of monitoring. Essential facilities are monitored more intensively, sometimes even without a specific reason. In the case of important facilities, supervision tends to take place when there are indications of problems. This logic is also reflected in German law, in the regulations for particularly important facilities (Section 61 BSIG) and important facilities (Section 62 BSIG).
Sanctions: which risks are realistic
What is the fundamental threat?
Sanctions do not only consist of fines. The law provides the BSI with a set of instruments consisting of supervisory and enforcement measures, and in addition, if orders are not complied with, administrative coercion is also possible, e.g. fines.
Fines: Scale and graduation
The fines are staggered depending on the category: For particularly important institutions, they can range up to €10 million or 2% of global annual turnover, for important institutions up to €7 million or 1.4%, whichever is higher. In its FAQ, the BSI expressly points out that fines are possible, for example, for breaches of reporting obligations.
What are the most common risks in practice?
Experience has shown that the realistic risk areas are not so much the theoretical maximum fines, but recurring basics that authorities and auditors can quickly address:
- Late or incomplete reports: Late or incomplete reports are a frequent risk, for example because internal coordination is still taking place, information from the service provider is missing or decisions take too long. The three-stage reporting system is clearly defined. Whether the deadlines are met therefore depends on well-established processes and 24/7 availability.
- Registration or change notifications not correct or not on time, in particular if affectedness was incorrectly assessed or not documented.
- Paper compliance without proof of effectiveness: Measures exist, but tests or evidence are lacking. This is critical because NIS-2 is aimed at resilience and demonstrable effectiveness, not just guidelines.
- Supply chain or service providers: Audits in particular quickly reveal whether the supply chain is really under control: Is there a list of critical service providers? Are security requirements regulated in the contract? Are incidents reported in good time? How are subcontractors dealt with and what evidence is available? This is exactly what NIS 2 explicitly expects as part of risk management.
Checks and audits: what companies should expect
- Audit intensity by category: In the case of particularly important facilities, the BSI can order audits, inspections or certifications in order to monitor the obligations. In the case of important facilities, audits are usually conducted on an ad hoc basis, i.e. if there are specific indications of breaches or gaps.
- KRITIS operators: formalized verification obligations: Evidence is particularly important for operators of critical systems: The BSIG contains its own obligations to provide evidence, which must be provided regularly. The procedure and requirements for evidence can be specified by the BSI.
- What do people typically want to "see" in audits? Audits rarely ask whether a specific tool is used. The decisive factor is whether security can be reasonably controlled and documented. There are typically four thematic blocks: Risk Management, Incident Response & Notifiability, Supply Chain and Governance or Training.
Implementation in practice
In practice, a procedure in three clear work packages has proven its worth:
- Determine affectedness & scope: Which organizational units, services and critical processes fall within the scope? This forms the basis for registration, priorities and subsequent verification.
- Gap analysis against the minimum catalog (§ 30 BSIG): Where do you stand in terms of risk analysis, incident handling, BCM, vulnerability management, access protection, MFA, effectiveness control, etc.?
- Implement in a verifiable manner: Don't just write guidelines, prove their effectiveness (e.g. restore tests, incident exercises, documented improvements).
NIS-2 explicitly requires supply chain security as part of risk management.
In practice, this means above all
- Identify critical service providers (cloud, hosting, MSP, MSSP, identity, email, ERP, remote maintenance, OT service) and classify them according to criticality.
- Define and contractually secure minimum requirements (MFA, privileged access, patch and vulnerability processes, logging, incident contact 24/7, BCM, recovery, evidence or reports).
- Ongoing review instead of one-off questionnaires (re-assessments, KPIs, change triggers for subcontractors or service changes).
The BSIG adopts the 24h / 72h / 1 month stage model. It is therefore crucial that a reliable internal picture of the situation is created quickly (affected systems or services, impact, initial hypothesis, measures, indicators if available), often with information from cloud or MSP environments.
Conclusion
NIS-2 makes cyber security mandatory for many companies, not only internally but also in the supply chain. It is crucial that risk management and emergency processes really work on a day-to-day basis: Those who can quickly classify and report incidents have a clear advantage. It is just as important to look at service providers such as cloud providers or managed services, because without reliable information from the supply chain, deadlines and measures can hardly be implemented properly. Those who clarify who is affected, responsibilities and minimum standards early on and implement them in a verifiable manner not only strengthen compliance, but above all their own resilience.
FAQ
The quickest way is to combine the sector, sub-sector and company size (employees, turnover, balance sheet total) as well as possible special cases (e.g. certain digital services). In Germany, the BSI impact assessment provides initial guidance. In the end, the classification according to BSIG or annexes is legally decisive.
This refers not only to suppliers of goods, but above all to IT and digital service providers who operate, maintain or have access to systems (cloud, MSP, hosting, software, remote maintenance). Subcontractors also play a role because risks are otherwise passed on. Transparency and rules on subcontractors are therefore important.
Critical providers are those that enable core processes or where a failure affects many systems simultaneously, e.g. cloud, hosting, identity, email, ERP, data center. Service providers with admin or remote access are also often considered critical because they have a direct impact on availability and security in the event of an incident.
Clear rules on incident information (who informs whom, how quickly, what content), 24/7 availability, as well as guidelines on vulnerability management, access protection, logging and evidence are important. Without these points, the information you need for 24/72-hour notifications is often missing in an emergency.
The deadline runs from the time when the incident was recognized internally as significant ("knowledge"), not only when everything has been clarified. The first report is about a quick classification: what happened (rough description), how critical it is, and whether a malicious background or cross-border effects are plausible.
Both should be based on a common incident setup: a picture of the situation, a coordinated set of facts and clear roles (security, legal, data protection). It is crucial that statements are consistent: NIS-2 focuses on the operational and security situation, GDPR on personal data and risks for data subjects. This often overlaps, but the addressees are different.
In principle, it is the affected institution, i.e. the company, that must comply with the obligations, even if the trigger lies with the provider. This is why contractual obligations to provide information quickly are so important. Depending on the situation, it may also be necessary to inform customers if services are impaired.
Typical requirements include evidence of risk analysis and action plans, incident and reporting processes (including exercises), BCMm backups, restore tests and supplier management (critical service provider list, minimum standards, contract clauses, evidence). Auditors look less at tools and more at whether processes work and can be documented.
This can be relevant, especially for certain digital services: an EU representative is often required and regulations apply depending on the main establishment or jurisdiction. In practice, contractual pressure also plays a major role: EU customers often demand NIS 2-compliant standards and evidence, even if the direct obligation is complex.
Firstly, clearly delineate who is affected and critical processes and define responsibilities. Secondly, establish reporting capability (24/72-hour situation report, escalation, 24/7 contact, templates). Thirdly, identify critical service providers and contractually define the most important minimum requirements so that incident information and access security are guaranteed.

Larissa Ragg
LinkedInMarketing Managerin · lawcode GmbH
Larissa Ragg verantwortet die Content-Strategie bei lawcode und erstellt Fachbeiträge zu den Themen EUDR, ESG-Compliance, HinSchG, Supply Chain und CSRD. Ihre Beiträge auf dem lawcode Blog machen komplexe regulatorische Anforderungen verständlich und liefern Unternehmen praxisnahe Orientierung.





